What is SOC 2: Your Ultimate Guide to SOC 2 Compliance
In this digital warfare, data security has become essential as the threat landscape is expanding exponentially. Today’s customers and businesses don’t trust promises alone. Instead, they require admissible evidence and proof regarding the organization’s compliance status and the security of their systems and networks.
In fact, cybersecurity has become a serious concern for all enterprises, including those that outsource key business operations to 3rd party vendors, such as SaaS and cloud computing providers. According to Cyber Management Alliance, on March 10, 2026, cybercriminals attacked a third-party service provider, gaining unauthorized access to the sensitive data of approximately 15,000 Ericsson customers.
Therefore, SOC 2 compliance has become more important than ever. However, you need the best SOC 2 audit services with automation platforms having licensed CPA partners.
In addition to ensuring compliance, the SOC 2 certification status will help prevent financial and reputational damage. This article will explore the SOC 2 compliance regime and guide you towards your successful SOC 2 journey. Here is some help!
What is SOC 2?
Service Organization Control (SOC) 2 is a cybersecurity compliance framework that outlines how enterprises should protect their digital assets from security incidents and data breaches.
The SOC 2 examination report on a service organization’s controls addresses five Trust Services Criteria (TSC):
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
The American Institute of Certified Public Accountants (AICPA) certifies assessors who then issue the independent third-party SOC 2 compliance reports.
In addition, there are two types of SOC 2 reports: SOC 2 Type I and SOC 2 Type II. Both reports assess the same criteria. However, the key differences between the two are the report’s thoroughness, cost, and length. The following table demonstrates the difference in detail.
| Type I | Type II | |
| Scope | Assess the design of controls | Test design of controls + operational effectiveness |
| Period | Assess controls at a single point in time | Assess controls over a period of time |
| Assurance Level | Moderate (provides a baseline) | Higher (more comprehensive) |
| Timeframe | Faster (often a few weeks to months) | Longer (6-12 months) |
| Testing Depth | Snapshot view | Demonstrates sustained control effectiveness |
| Cost | Cheaper | Expensive |
What is a SOC 2 Audit?
Each organization has its own security controls to comply with SOC TSC. Therefore, security controls and attestation reports are unique to every company.
An independent SOC 2 auditor will assess an organization’s security with respect to one or more of these TSC. After that, the business put internal controls in place to ensure they meet SOC 2 compliance requirements. After completing the audit, the auditor will write a report about how well the organization’s IT environment adheres to SOC 2 TSC.
In addition, the auditor also delivers a full SOC 2 report to the organization in question, whether they pass the audit or not. The Auditor uses some terms to describe the audit results. These terms are described below.
SOC 2 Audit Checklist
The SOC 2 Audit Checklist is a roadmap that breaks down your company’s compliance preparation into manageable tasks. It elaborates on the entire process of your organization’s compliance journey.
Moreover, the audit checklist will help you define your organization’s audit scope and objectives, identify gaps, track evidence, and assign ownership of compliance-related tasks.
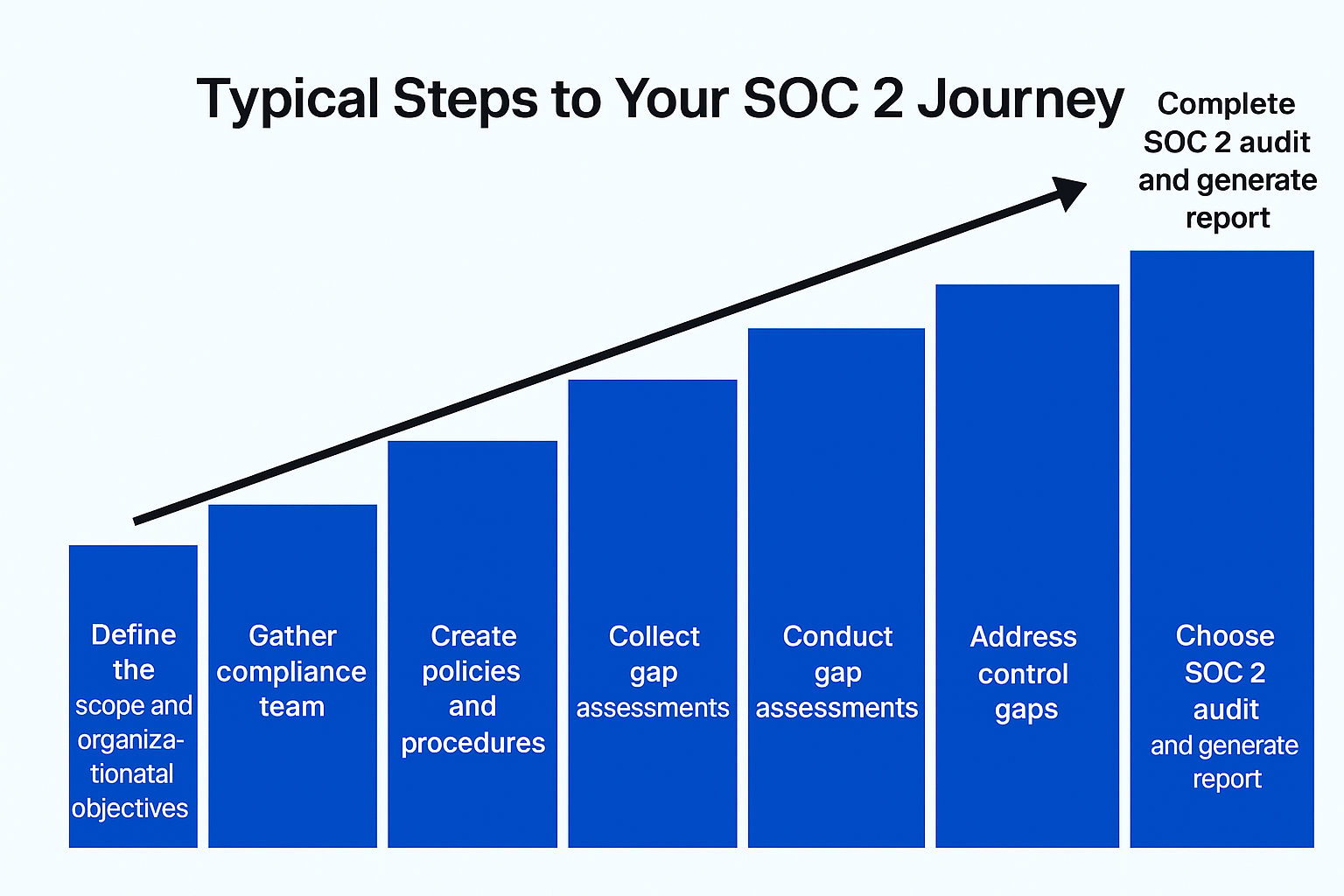
Typical Steps to Your SOC 2 Journey
Your compliance partner company performs an SOC 2 assessment and tests the operational effectiveness of your security controls. These practices involve a clear number of steps required to achieve SOC 2 compliance objectives.
- Define scope and organizational objectives
- Gather the compliance team
- Communicate plans internally
- Create policies and procedures
- Collect evidence
- Perform risk assessments
- Conduct gap assessments
- Address control gaps
- Choose SOC 2, auditor
- Complete SOC 2 audit and generate a report
If you need an SOC 2 report in a cost-effective and timely manner, you need a reliable, trustworthy company like Sigma Technology Partners.
Which Companies Are Eligible for a SOC 2 Report?
Organizations that store, process, or transmit customers’ data must acquire a SOC 2 compliance report. SOC 2 compliance will help you build trust with customers who already demand this report. Moreover, your customers will know that their data is safe under appropriate security controls.
Various types of companies and enterprises need SOC 2 compliance. These companies include:
- Businesses selling to the government or enterprises
- Fintech companies
- IT service companies and Managed Services Providers (MSPs)
- Data centers and cloud service providers
- SaaS companies
Performing SOC 2 Audit: CPA Services
To attest to the SOC 2 report, a CPA partner accredited by the AICPA is always mandatory. The compliance analysts recommend selecting a partner that has its own audit management platform.
Sigma Technologies Partners has a licensed CPA partner who performs an independent attestation for your SOC 2 report.
SOC 2 Compliance Automation
Businesses always prefer choosing a compliance automation software suite for their SOC 2 compliance journey. It will save a significant amount of time and money for your SOC 2 certification.
In addition to being a licensed CPA partner, Sigma Technologies Partners also offers compliance automation and Governance, Risk, and Compliance (GRC) software platform that includes CyberGuard, SurfaceGuard, SecureSight, and RiskVision.
Conclusion
This article has taken a deep dive into the SOC 2 compliance regime. It concludes that SOC 2 certification has become more vital than ever due to ever-increasing cybersecurity threats and attacks.
If your organization falls prey to a data breach, you will face heavy penalties, financial issues, customer distrust, and reputational damage.
When looking for an SOC 2 audit report, ensure you contact the right company with a licensed CPA partner.
FAQs
What is SOC 2?
SOC 2 is a cybersecurity compliance framework that defines how well organizations protect their digital assets from security incidents and data breaches. SOC 2 has five Trust Services Criteria (TSC): security, confidentiality, processing integrity, availability, and privacy.
Why Should I Need a SOC 2 Compliance?
You need SOC 2 compliance to protect your customers’ data from notorious cyber threats and attacks. Noncompliance can result in heavy penalties, customers’ distrust, financial issues, and reputational damage.
Why Does CPA Partner Matter?
A licensed CPA partner is mandatory to independently attest to a SOC 2 report. He is accredited by the AICPA. Hence, organizations should look for a SOC 2 services company that has a licensed CPA partner.
Are there Any Tools for Compliance Automation?
Yes, compliance automation tools are available in the cybersecurity market. However, you need one that is fast and reliable, offering automated policies, evidence collection, AI Assessments, e-signatures, and so forth. Sigma Technology Partners’ CyberGuard.ai tool offers all these features.
Sigma Technologies Partners – Your First and Best Bet
Sigma Technologies Partners offers world-class compliance automation and security tools, including CyberGuard.ai, SurfaceGuard, SecureSight, and RiskVision. This software suite not only helps you obtain your SOC 2 compliance report but also builds customer trust and prevents reputational issues.
We are a reliable and trustworthy partner. Partner with us and get a licensed AICPA-accredited CPA for independent attestation. In addition, we offer powerful compliance automation through our CyberGuard.ai tool.
In addition, Cyberguard.ai automates policies and procedures, evidence collection, e-signature and acknowledgment, gap assessments, and audit readiness. It will save you significant time and money.
Book your free CyberGuard.ai demo now or speak with our SOC 2 experts.
Your customers are already asking for SOC 2 proof. Make sure you’re ready to deliver it — confidently and efficiently.